Chinese Facial Recognition Database Leak Sparks Mass Data Collection Fears
A Chinese company running facial recognition systems exposed the personal information of 2.5 million people by leaving a database unprotected.
Discovery of the Leak
Victor Gevers, a Dutch cybersecurity expert at the GDI Foundation, discovered the unprotected database. He tweeted about SenseNets, a Chinese company producing AI-based security software for face recognition, crowd analysis, and identity verification. “Anyone could access their business IP and millions of people tracking data,” Gevers noted.
Details of the Exposed Data
The database included ID card numbers, tracking location data from the last 24 hours, sex, nationality, address, passport photos, birthdays, and employers. Gevers first notified SenseNets about the issue in July. Although SenseNets later secured the database with a firewall, the data had already leaked.
Understanding the Chinese Social Credit System
The Chinese social credit system is a nationwide initiative to enhance trust and compliance among citizens and businesses. It combines various data sources to create a comprehensive score reflecting an individual’s or entity’s behaviour.
How It Works
The social credit system monitors a wide range of activities, including:
- Financial Behavior: It tracks loan repayments, credit card usage, and other financial transactions.
- Legal Compliance: It records adherence to laws and regulations, including traffic violations and court judgments.
- Professional Conduct: It evaluates performance and behaviour in professional settings, including contractual obligations and industry-specific regulations.
- Social Behavior: It monitors community involvement, social media usage, and interpersonal interactions.
The data is collected from government databases, private companies, and public sources. Advanced technologies like facial recognition, big data analytics, and artificial intelligence analyze this information to assign scores.
Impact of the Social Credit Score
A high social credit score can lead to numerous benefits, such as:
- Access to Loans: Easier approval for loans and lower interest rates.
- Travel Privileges: Faster visa processing and access to VIP airport lounges.
- Job Opportunities: Better job prospects and preferential treatment in hiring.
Conversely, a low social credit score can result in severe penalties, including:
- Restricted Travel: Bans on buying plane and train tickets.
- Reduced Employment Opportunities: Difficulty in finding jobs or career advancement.
- Limited Access to Public Services: Restrictions on accessing certain public services and social benefits.
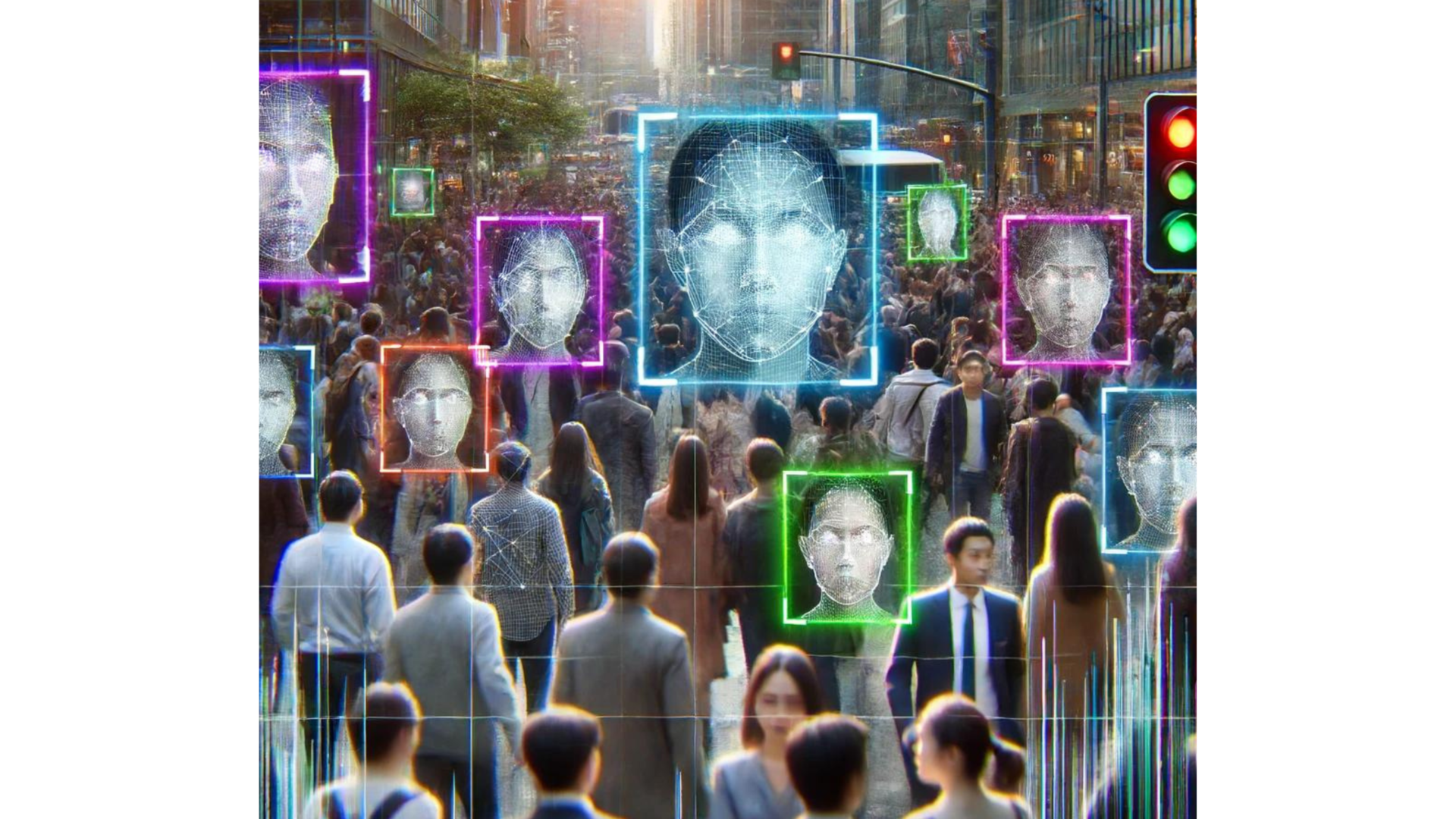
Integration with Facial Recognition
Facial recognition technology is a critical component of the social credit system. It enhances the monitoring and enforcement capabilities by:
- Identifying Individuals in Public Spaces: Cameras equipped with facial recognition software track and identify people in real time.
- Linking Behavior to Identity: The system links observed behaviours to individuals’ social credit scores, ensuring accurate and comprehensive monitoring.
- Predicting and Preventing Crime: The technology helps predict potential criminal activities, allowing authorities to intervene preemptively.
Prevalence of Surveillance in China
China is known for its extensive surveillance network, which is one of the most advanced and comprehensive in the world. The government uses technology extensively for monitoring and controlling the population, incorporating various methods and tools to ensure public compliance and safety.
Scale and Scope of Surveillance
China’s surveillance infrastructure includes millions of cameras, often equipped with facial recognition technology. These cameras are strategically placed in urban areas, public spaces, transportation hubs, and schools. The goal is to monitor and record every aspect of public life, providing authorities with real-time data.
- Facial Recognition Cameras: An estimated 200 million CCTV cameras are in use, many of which are equipped with advanced facial recognition software. These cameras can identify individuals, track their movements, and predict behaviour.
- Social Media Monitoring: The government monitors social media platforms to track public opinion and identify dissent. Automated systems analyze posts, messages, and interactions to flag potential threats.
- Mobile Tracking: Authorities use mobile phone data to track individuals’ locations and movements. This data, combined with other surveillance methods, allows for comprehensive monitoring.
- Internet Surveillance: China’s “Great Firewall” controls and filters internet content, restricting access to information and monitoring online activities. The government employs sophisticated techniques to censor and surveil internet usage.
Impact on Daily Life
Pervasive surveillance significantly impacts the daily lives of Chinese citizens. It influences behaviour, as people know they are constantly being watched. This awareness can lead to self-censorship and a reduction in activities deemed undesirable by the government.
- Public Behavior: People avoid actions that could negatively impact their social credit score or attract government scrutiny. This includes limiting participation in protests, avoiding controversial discussions online, and adhering to social norms.
- Privacy Concerns: Extensive surveillance raises significant privacy issues. Many citizens are concerned about the government’s ability to intrude into their personal lives and the potential misuse of collected data.
Government Justifications
The Chinese government justifies its extensive surveillance network by emphasizing public safety, crime prevention, and social stability. Authorities claim that the system helps to reduce crime rates, enhance public security, and maintain social order.
- Crime Prevention: Surveillance helps identify and apprehend criminals quickly, reduce crime rates, and improve public safety.
- Social Order: Monitoring ensures compliance with laws and regulations, helping to maintain social harmony and stability.
International Reactions
The international community has mixed reactions to China’s surveillance practices. Human rights organizations criticize the government’s approach, citing concerns about privacy violations and potential abuse. Some countries fear that China’s model could influence other governments, leading to a global increase in surveillance and control.
- Human Rights Concerns: Organizations like Amnesty International and Human Rights Watch frequently criticize China’s surveillance state for violating privacy rights and freedom of expression.
- Influence on Other Nations: There are concerns that other authoritarian regimes might adopt similar surveillance techniques, leading to a broader erosion of privacy rights worldwide.
Sensitive Nature of Facial Recognition Data
Facial recognition data is susceptible and needs robust protection. Organizations must protect this data to avoid severe penalties. Here are some key points to consider:
- Biometric Permanence: Unlike passwords or PINs, biometric data such as facial features cannot be changed. Once compromised, the data remains vulnerable.
- Privacy Risks: Misuse of facial recognition data can lead to unauthorized surveillance, identity theft, and personal privacy violations.
- Accuracy Concerns: Errors in facial recognition technology can result in false positives, leading to wrongful accusations or detentions.
- GDPR Regulations: The General Data Protection Regulation (GDPR) mandates strict guidelines for handling biometric data in Europe. Companies must comply with these regulations to avoid heavy fines.
- Security Breaches: Unprotected databases can be hacked, exposing sensitive information widely. Companies must implement robust security measures to safeguard data.
- Data Misuse: Governments or organizations may misuse facial recognition data for unauthorized purposes, such as political surveillance or discrimination.
- Ethical Considerations: Facial recognition technology raises moral questions about consent, transparency, and the right to privacy.
- Public Trust: The exposure of sensitive data can erode public trust in technology and the organizations that deploy it. Ensuring data security is crucial for maintaining this trust.
Handling Sensitive Data
Javvad Malik from AlienVault underscores the dangers of storing sensitive data. Unlike passwords, biometric data like faces cannot be changed easily. Malik advises companies to integrate security and privacy controls at every stage, from development to deployment.
Users must remain cautious as governments and businesses collect vast amounts of data, including facial recognition trials in public places. Ultimately, those implementing these programs must ensure the data is secure. Failure to do so can have severe consequences.
Conclusion
The Chinese facial recognition database leak highlights vulnerabilities in handling sensitive data. As the Chinese social credit system demonstrates, integrating facial recognition with other data can have significant implications. Ensuring robust security measures is critical to protecting this data and preventing misuse. As technology advances, the balance between surveillance and privacy remains crucial.
If you would like to work with a professional team that can help make your transition to a life of freedom, contact Amicus Int. for New Identity services today.